Of course. Let's break down GetCkVdValue in detail.
What is GetCkVdValue?
GetCkVdValue is a custom PHP function that is not part of the native PHP or DedeCMS core. It was created specifically for the DedeCMS (织梦CMS) system to solve a very common security problem.
Its primary purpose is to decrypt (decode) values that were encrypted by the GetCkVdValue() function (the original version of this function).
The Problem It Solves: Anti-Spam Tokens
In web development, especially for content management systems like DedeCMS, forms are a prime target for spammers. These bots can automatically submit forms to post comments, send messages, or create junk content.
To prevent this, developers use anti-spam tokens. The process looks like this:
- Generate a Token: When a page with a form loads, the server generates a unique, random value (a token). This token is often stored in the user's session.
- Send the Token: The server includes this token as a hidden field in the HTML form.
- Encrypt the Token (Optional but common): For an extra layer of security, the token is encrypted using a secret key before being sent to the browser. This makes it harder for bots to guess or manipulate.
- Submit the Form: The user fills out the form and submits it. The browser sends the form data, including the encrypted token, back to the server.
- Decrypt and Verify: The server receives the form data. It uses a function like
GetCkVdValueto decrypt the token. It then compares this decrypted token with the one it stored in the session. If they match, the form submission is considered legitimate. If not, it's rejected as spam.
GetCkVdValue is the server-side function responsible for Step 5: Decryption.
How It Works (The Technical Details)
The GetCkVdValue function is typically found in a core DedeCMS file, most commonly:
/include/helpers/extend.helper.php
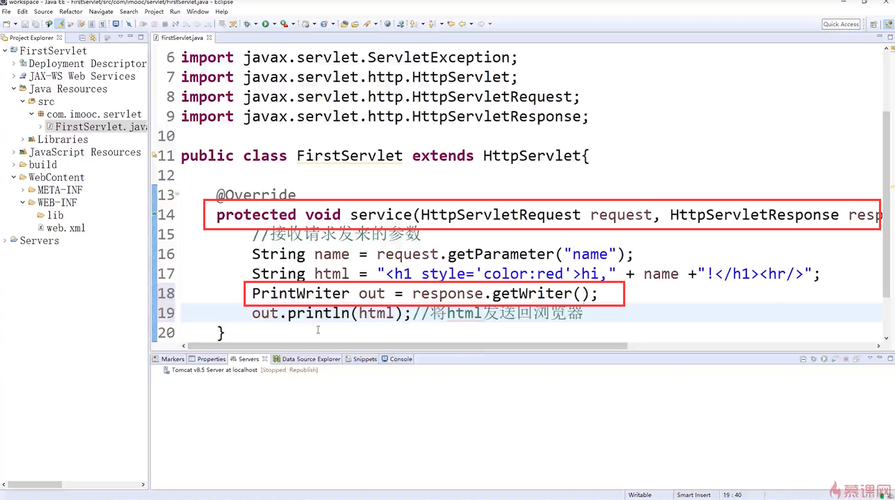
Here is a typical implementation of the function:
/**
* 解密验证码值
*
* @param string $ckey 加密后的字符串
* @return string|null 解密后的原始值,如果失败则返回null
*/
function GetCkVdValue($ckey)
{
// 1. 定义加密密钥 (这个密钥必须与加密时使用的密钥完全相同)
$key = '!@#$%^&*()';
// 2. 对密钥进行MD5哈希,确保密钥长度固定
$cryptkey = md5($key);
// 3. 解密过程:使用Base64解码
$keya = md5(substr($cryptkey, 0, 16));
$keyb = md5(substr($cryptkey, 16, 16));
$keyc = substr($ckey, 0, 4);
$cryptkey = $keya . md5($keya . $keyc);
$ckey_length = strlen($ckey);
$string = '';
$length = 0;
for ($i = 0; $i < $ckey_length; $i++) {
if ($i < $ckey_length) {
$string .= $ckey{$i} ^ $cryptkey{$i % 32};
}
}
$string = substr($string, 4);
// 4. 校验和验证
$validate = substr($string, 0, 16);
$string = substr($string, 16);
// 如果校验失败,返回空
if ($validate !== substr(md5($string . $keyb), 0, 16)) {
return '';
}
// 5. 返回解密后的值
return $string;
}
Step-by-Step Breakdown:
- Key Definition:
$key = '!@#$%^&*()';This is the secret "password" used for both encryption and decryption. This key must be the same in both the encryption and decryption functions. - Key Preparation: The raw key is hashed with
md5()to create a consistent 32-character string ($cryptkey). - Decryption Logic:
- It splits the
$cryptkeyinto two parts,$keyaand$keyb. - It extracts a 4-character prefix from the incoming encrypted data (
$keyc). This prefix is crucial as it was added during encryption to make each encrypted result unique, even if the original data is the same. - It reconstructs the full decryption key (
$cryptkey) using$keyaand the extracted$keyc. - It then iterates through the encrypted string (
$ckey) and uses the XOR (^) operation to reverse the encryption process, restoring the original data.
- It splits the
- Validation:
- After decrypting, a 16-character checksum (
$validate) that was added at the beginning of the original data is checked. - The function recalculates what the checksum should be using the decrypted data and the
$keyb. - If the original checksum doesn't match the recalculated one, it means the data was tampered with or the key is wrong, and the function returns an empty string.
- After decrypting, a 16-character checksum (
- Return Value: If the validation passes, the function returns the clean, decrypted string.
How to Use It
You will almost never call GetCkVdValue directly in a template file (*.htm). You call it in a PHP script that processes the form submission.
Example Scenario: Processing a Comment Form
-
When the page loads (
article_article.htm): A PHP script (e.g.,plus/feedback.php) generates a token, encrypts it, and passes it to the template.// In a PHP file that loads the template $token = 'some_unique_user_id_or_random_string'; $encrypted_token = GetCkVdValue($token); // Note: The function name is the same, it acts as both encoder and decoder $dtp->Assign('token', $encrypted_token); -
In the HTML Template (
article_article.htm): The encrypted token is placed in a hidden input field.<form action="/plus/feedback.php" method="post"> <input type="hidden" name="token" value="{dede:global.token/}"> <textarea name="msg"></textarea> <button type="submit">Submit Comment</button> </form> -
When the form is submitted (
plus/feedback.php): The processing script receives the form data and decrypts the token to verify it.// In plus/feedback.php or similar processing file require_once(dirname(__FILE__) . "/../include/common.inc.php"); require_once(DEDEINC."/helpers/extend.helper.php"); if (empty($_POST['token'])) { die('Error: Token is missing.'); } // Decrypt the token received from the form $submitted_token_value = GetCkVdValue($_POST['token']); // Now, verify the decrypted token against the one stored in the session // (This part is conceptual; DedeCMS has its own session logic) if ($submitted_token_value !== $_SESSION['vdcode']) { die('Error: Invalid token. Possible spam attempt.'); } // If we reach here, the token is valid. Proceed with processing the comment. // ... save comment to database ...
Summary
| Feature | Description |
|---|---|
| Type | Custom PHP function in DedeCMS. |
| Location | Usually /include/helpers/extend.helper.php. |
| Purpose | To decrypt a string that was encrypted for anti-spam verification. |
| Mechanism | Uses a secret key, XOR operations, and checksum validation. |
| Common Use | Verifying tokens in comment forms, contact forms, and other user-submission areas to prevent bot spam. |
| Key Dependency | The secret key used for decryption must be identical to the one used for encryption. |




